Identifying Cyber Vulnerabilities in Manufacturers Digital Supply Chain Networks

The fourth industrial revolution brings a new operational risk for smart manufacturers and digital supply networks: cyber, and in the age of Industry 4.0, cybersecurity strategies should be secure, vigilant, and resilient, as well as fully integrated into organizational strategy from the start.
The interconnected nature of Industry 4.0–driven operations and the pace of digital transformation mean that cyberattacks can have far more extensive effects than ever before, and manufacturers and their supply networks may not be prepared for the risks.
For cyber risk to be adequately addressed in the age of Industry 4.0, cybersecurity strategies should be secure, vigilant, and resilient, as well as fully integrated into organizational and information technology strategy from the start.
A new study conducted by Deloitte confirms what many supply chain managers have long suspected: Cyber breaches are on the rise for major companies.
According to Deloitte, the U.S. manufacturing sector is “woefully unprepared” for the cyber threats associated with new connected technology.
In the study “Industry 4.0 and cyber risk: Security in an age of connected production,” one-third of all manufacturers sampled admitted to not having performed any cyber risk assessments of the industrial connected devices operating on factory floors.
René Waslo, a cyber risk principal with Deloitte, says that in the age of “Industry 4.0,” we’re only beginning to understand the power that connected devices will have over our lives.
“The financial services and life sciences sectors are probably the most refined in their understanding on how to protect the attack surface,” she says, “but other industries must quickly come up to speed.”
The new Deloitte study outlines the strategies that businesses must take to build cybersecurity efforts into their larger business plan and untimely protect their operations and their customers.
“Even in an era when companies may anticipate less regulatory oversight, the incentives for protecting brand by fully identifying threat vectors is obvious,” she adds.
Key insights on some of the most significant cyber challenges manufacturers must address include:
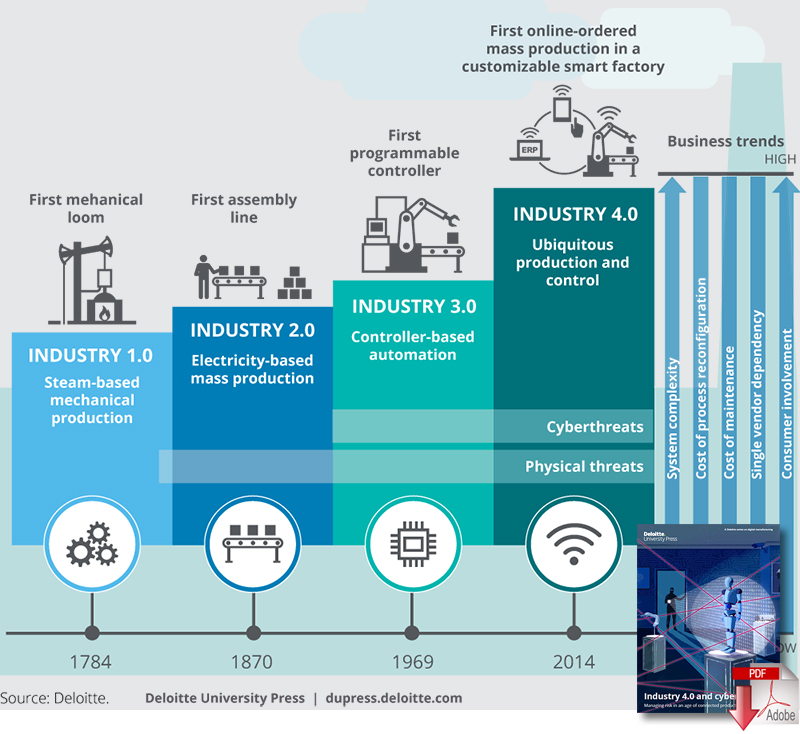
- Evolution of Cyber Risks from I3.0 to I4.0 – New cyber threats facing Industry 4.0 have built upon common Industry 3.0 attacks with malicious marketing campaigns, disruption of service attacks using botnets and privacy breaches, including the compromise of sensitive customer data and trade secrets, becoming top concerns.
- More IoT Devices Equals More Vulnerabilities – Over 20 billion IoT devices are expected to be deployed around the world by 2020, with many of these devices being used in manufacturing facilities and production lines. As these devices are integrated further, manufacturers will need to implement their own safeguards and security practices to protect their operations and those that they depend on from third-parties.
- Learnings From Other Industries Need to be Leveraged – As manufacturing has been behind the curve in adopting connected technology compared to other industries, learnings from other sectors like financial services should be incorporated into manufacturing strategies.
Finally, Deloitte believes new technologies like blockchain have the potential to help mitigate current cybersecurity risks by streamlining the flow of goods and information.
The process of establishing a historical record for currency is best known in the example of bitcoin, but other organizations are exploring ways to use this new tool to determine the flow of goods from production line through layers of purchasers.
Creating a historical ledger that is shared by a community establishes trust and visibility, providing protection for buyers and sellers by certifying a good’s authenticity, enabling the tracking of goods movements for logistical purposes, and categorizing products more specifically than by lots or batches when handling recalls or defects.
In the absence of this level of assurance of product authenticity, manufacturers may want to perform testing and certification of products to ensure adequate security before incorporating them into their environment or products.
Progression of cyber and physical threats for each industrial revolution
Article Topics
Deloitte News & Resources
MHI Report: Investment increases as supply chains become more tech-forward and human-centric Global Trade Tensions, Material Shortages Not Expected to Ease in 2024 Blockchain in Supply Chain Continues to Mature Supply Chains Struggle to Access Reliable Emissions Data from Suppliers State of the industry: MHI releases annual report at ProMat 2023 MHI and Deloitte launch 2023 Annual Industry Report survey How Amazon Is Preparing For Fully-Electric Drone Delivery More DeloitteLatest in Technology
Happy Returns Partners With Shein and Forever 21 to Simplify Returns Frictionless Videocast: AI and Digital Supply Chains with SAP’s Darcy MacClaren The Top 10 Risks Facing Supply Chain Professionals Walmart’s Latest Service: Ultra Late-Night Delivery South Korea Finally Overtakes China in Goods Exported to U.S. SAP Unveils New AI-Driven Supply Chain Innovations U.S. Manufacturing is Growing but Employment Not Keeping Pace More TechnologyAbout the Author