Massive Cyber Attack Hits Businesses Worldwide
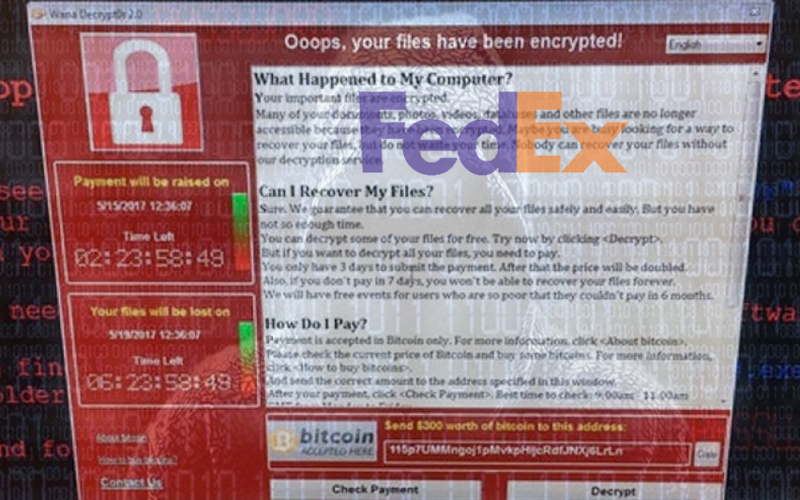
A massive cyber-attack using tools believed to have been developed by the US National Security Agency has struck organizations around the world, including the USA, UK, Spain, Russia, China, Portugal and Sweden, experts say it may be the biggest ransomware attack ever observed.
A new strain of ransomware raced across 70 countries Friday, wreaking havoc at the National Health Service in the UK, hobbling one of Spain’s largest telecom companies, and shutting down Russia’s Internal Affairs Ministry in an attack that cybersecurity experts say is only gaining in momentum.
Ransomware is a type of malware that installs itself on a device, such as a computer or smartphone, and then holds the device hostage until a ransom is paid.
This particular strain, WannaCry, exploits a vulnerability in Windows that many systems have not yet patched.
WannaCry has so far infected tens of thousands of computers in at least 74 countries, according to cybersecurity companies who are observing its spread across the globe.
Among the countries infected are the US, China, Russia, Spain, and the UK.
Ransomeware: Who's Affected & Why
Kaspersky Lab's Global Research & Analysis Team reported “earlier today, our products detected and successfully blocked a large number of ransomware attacks around the world. In these attacks, data is encrypted with the extension “.WCRY” added to the filenames.”
Kaspersky Lab's analysis indicates the attack, dubbed “WannaCry”, is initiated through an SMBv2 remote code execution in Microsoft Windows. This exploit (codenamed “EternalBlue”) has been made available on the internet through the Shadowbrokers dump on April 14th, 2017 and patched by Microsoft on March 14.
Unfortunately, it appears that many organizations have not yet installed the patch.
FedEx Hit
American shipping giant FedEx has been hit in a ransomware attack spreading quickly around the globe and linked to hacked or leaked data from the U.S. National Security Agency.
FedEx confirmed early Friday afternoon that it was a victim of the attack, but disclosed few details.
“Like many other companies, FedEx is experiencing interference with some of our Windows-based systems caused by malware,” the firm said in a statement.
“We are implementing remediation steps as quickly as possible. We regret any inconvenience to our customers.”
Latest News: Researchers See Possible North Korea Link to Global Cyber Attack
What you need to do: If you've not installed the March, April or May Windows Update bundles, do so immediately. It's worth shutting down your system for a few minutes if it gives you a chance to avoid this. If you're still using Windows XP, you're out of luck, but the March and April update bundles should be available to Windows Vista. What Is Ransomware and How Can I Protect Myself?
More: Security Awareness Training Blog
Meanwhile, NSA whistleblower Edward Snowden has led the discussion on NSA’s role and responsibility in Friday’s extensive cyberattacks, noting that if the NSA had “privately disclosed the flaw used to attack hospitals when they found it, not when they lost it, this may not have happened.”
If NSA builds a weapon to attack Windows XP—which Microsoft refuses to patches—and it falls into enemy hands, should NSA write a patch? https://t.co/TUTtmc2aU9
— Edward Snowden (@Snowden) May 12, 2017
Ransomware is one of the fastest-growing types of cyberattacks. Last year, cybersecurity companies estimated that ransomware attacks brought in over a billion dollars for cybercriminal networks globally, and they are on target to make even more in 2017.
While hospitals were not the target of the WannaCry ransomware strain Friday, they were among the most infected as they often lack budgets to defend their online systems, and once their networks are down, thousands of patients lives may be put at risk. Across the UK Friday, doctors reported chaotic situations, with one tweeting that patients would die as a result of the attack.
“This attack was not specifically targeted at the NHS and is affecting organisations from across a range of sectors,” the NHS said in a statement. “Our focus is on supporting organisations to manage the incident swiftly and decisively.” NHS cyber-attack: Amber Rudd says lessons must be learnt
Cybersecurity experts said Friday that the Wannacry ransomware shows no signs of slowing down. Preliminary research on the strain shows that it is able to run in 27 languages, and likely includes other vulnerabilities that can take advantage of systems.
For now, cybersecurity experts are urging people to download the Microsoft update which patches the vulnerability as soon as possible to make sure their systems are protected.
Update: Security Blogger Halts Ransomware 'By Accident'
Related Article: Identifying Cyber Vulnerabilities in Manufacturers Digital Supply Chain Networks
Article Topics
Deloitte News & Resources
MHI Report: Investment increases as supply chains become more tech-forward and human-centric Global Trade Tensions, Material Shortages Not Expected to Ease in 2024 Blockchain in Supply Chain Continues to Mature Supply Chains Struggle to Access Reliable Emissions Data from Suppliers State of the industry: MHI releases annual report at ProMat 2023 MHI and Deloitte launch 2023 Annual Industry Report survey How Amazon Is Preparing For Fully-Electric Drone Delivery More DeloitteLatest in Technology
Biden Gives Samsung $6.4 Billion For Texas Semiconductor Plants Apple Overtaken as World’s Largest Phone Seller Walmart Unleashes Autonomous Lift Trucks at Four High-Tech DCs Talking Supply Chain: Procurement and the AI revolution 80% of Companies Still Unsure How to Best Leverage AI, Study Finds Supply Chain Stability Index: “Tremendous Improvement” in 2023 AI Not a Priority for Retailers and CPG Companies More Technology