Cyber Attacks Targeting Smartphone Supply Chains

A new mobile trojan dubbed “DeathRing” is being pre-loaded on to smartphones somewhere in the supply chain, warn researchers at mobile security firm Lookout.
DeathRing is a Trojan believed to be of Chinese origin that masquerades as a ringtone app, but can download SMS and browser content from its command and control server to the victim’s phone.
DeathRing could use SMS content to phish a victim’s personal information, for example, using fake text messages requesting the data.
The malware could also use browser content to prompt victims to download further Android application packages (APKs), which may include more malware.
Lookout researchers say the malicious app is impossible to remove because it is pre-installed in the system directory.
This is of concern to original equipment makers (OEMs) and retailers because the compromise of mobiles in the supply chain could have a significant impact on customer loyalty and trust in the brand.
Mainly affecting lower-tier smartphones bought in Asian and African countries, this is the second significant example of pre-installed mobile malware that Lookout has found on phones in 2014.
The devices pre-loaded with DeathRing are so far mostly from third-tier manufacturers. The main countries affected are Vietnam, Indonesia, India, Nigeria, Taiwan and China.
Researchers said this signals a potential shift in cyber-criminal strategy towards distributing mobile malware through the supply chain.
Earlier this year, Lookout detected another pre-loaded piece of malware called Mouabad. Like DeathRing, Mouabad was also pre-installed somewhere in the supply chain and affected predominantly Asian countries, but researchers did see some cases in Spain.
Although it is impossible to remove DeathRing and Mouabad because they are pre-installed in the phone’s system directory, Lookout researchers recommend that mobile users:
- Be aware of the origins of the device they are buying.
- Download a mobile security app to protect against malware.
- Check phone accounts regular for any unusual charges.
Source: ComputerWeekly
Related: Regin, a New Computer Spying Bug Discovered

Article Topics
Lookout News & Resources
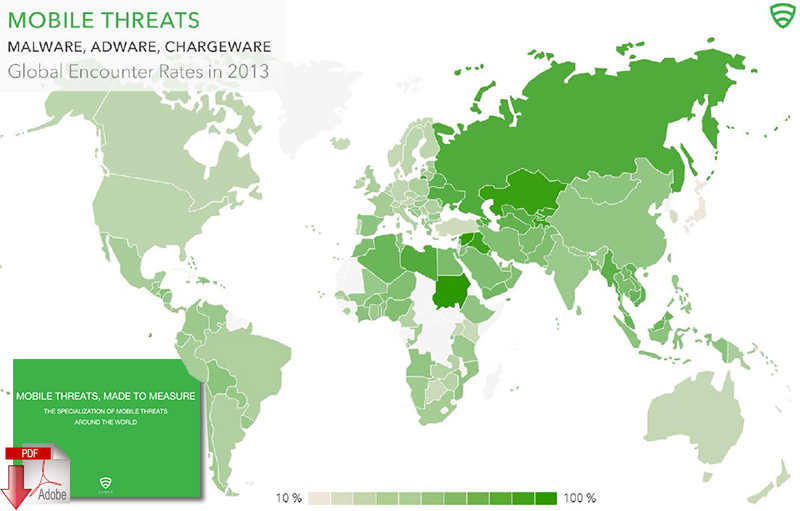
Mobile Threats, Made to Measure Cyber Attacks Targeting Smartphone Supply ChainsLatest in Technology
Spotlight Startup: Cart.com is Reimagining Logistics Walmart and Swisslog Expand Partnership with New Texas Facility Taking Stock of Today’s Robotics Market and What the Future Holds Biden Gives Samsung $6.4 Billion For Texas Semiconductor Plants Apple Overtaken as World’s Largest Phone Seller Walmart Unleashes Autonomous Lift Trucks at Four High-Tech DCs Talking Supply Chain: Procurement and the AI revolution More Technology